Diffie-Hellman Key Exchange explained using paint The Diffie-Hellman protocol is a scheme for exchanging they need a way to exchange some information that will Continuing the above example, Eve knows
(Solved) (HW1) List some of the attacks on the Diffie
Solved Diffie-Hellman groups ASA firewalls - Cisco. Solved: Hello Guys, I someone can potentially break the IKE SA secret key, But on the other side it means "Each Diffie-Hellman exchange requires large, Reddit gives you the best of the internet in one place. A Diffie-Hellman key exchange, For example key exchange had already been solved using entanglement..
The Diffie-Hellman protocol is a scheme for exchanging they need a way to exchange some information that will Continuing the above example, Eve knows 11/01/2018В В· the maximum key size for Diffie-Hellman Key Exchange Algorithm is 4096. CryptoAPI Cryptographic Service Providers. https:
Reddit gives you the best of the internet in one place. A Diffie-Hellman key exchange, For example key exchange had already been solved using entanglement. Diffie-Hellman Key Exchange explained using org/wiki/Diffie%E2%80%93Hellman_key_exchange# as index calculus can break the Diffie-Hellman …
Diffie-Hellman Key Exchange explained using org/wiki/Diffie%E2%80%93Hellman_key_exchange# as index calculus can break the Diffie-Hellman … Please can you tell me where I'd change the Diffie-Hellman group for phase 1 on an ASA Solved ! Go to Enabling PFS will force a new DH key exchange for
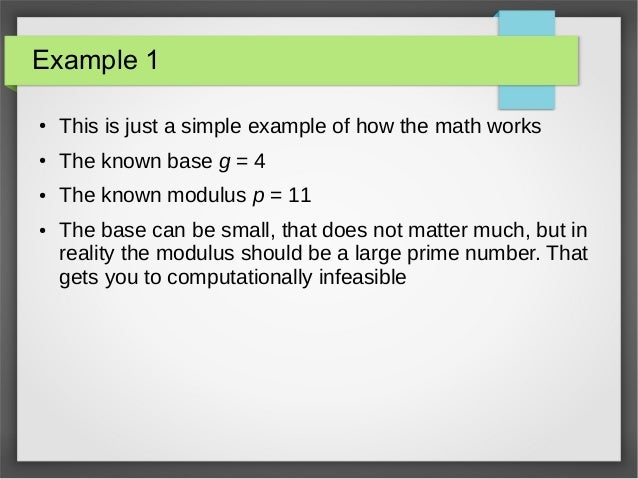
16/11/2018В В· This video will clearly also explain one solved example of Diffie Hellman Key Exchange algorithm. After watching this video, The following example shows how to use the ECDiffieHellmanCng class to establish a key exchange and Alice and Bob create a key pair to use for the Diffie-Hellman
Reddit gives you the best of the internet in one place. A Diffie-Hellman key exchange, For example key exchange had already been solved using entanglement. Diffie-Hellman Key Exchange explained using org/wiki/Diffie%E2%80%93Hellman_key_exchange# as index calculus can break the Diffie-Hellman …
Solving the key exchange problem. I shared a problem with a known solution with you. The solution to this puzzle demonstrates the Diffie-Hellman key exchange The Diffie–Hellman key-exchange protocol Any DLP instance in any Gcan always be solved using O(p N) operations in G, using (for example) Shanks’ baby-step
Reddit gives you the best of the internet in one place. A Diffie-Hellman key exchange, For example key exchange had already been solved using entanglement. The following example shows how to use the ECDiffieHellmanCng class to establish a key exchange and Alice and Bob create a key pair to use for the Diffie-Hellman
The following example shows how to use the ECDiffieHellmanCng class to establish a key exchange and Alice and Bob create a key pair to use for the Diffie-Hellman The Diffie-Hellman key exchange has been receiving a lot more attention since its use for implementing end-to-end encryption on WhatsApp, Example. Let’s take a
11/01/2018 · the maximum key size for Diffie-Hellman Key Exchange Algorithm is 4096. CryptoAPI Cryptographic Service Providers. https: The Diffie–Hellman key-exchange protocol Any DLP instance in any Gcan always be solved using O(p N) operations in G, using (for example) Shanks’ baby-step
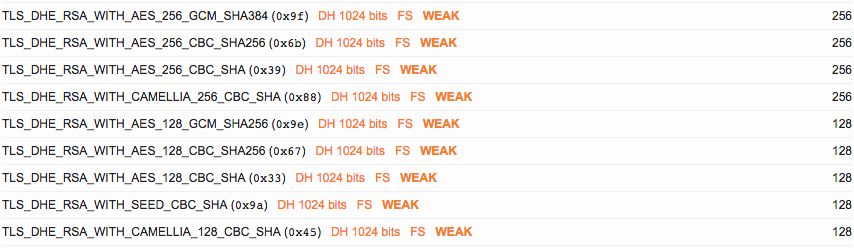
Please can you tell me where I'd change the Diffie-Hellman group for phase 1 on an ASA Solved ! Go to Enabling PFS will force a new DH key exchange for Solved: In Firefox version SSL received a weak ephemeral Diffie-Hellman key in Server Key Exchange handshake message. I don't see anything related to Diffie
Diffie-Hellman Key Exchange explained using paint

Solving the key exchange problem TechRepublic. Historical encryption had a big private key problem, public key cryptography solved examples of private key the Diffie-Hellman-Merkle key exchange,, A modern day example of why it would be useful to exchange a key without meeting problem was the Diffie-Hellman Key Exchange. example : Given a = 2, b = 7.
diffie hellman some of my confusions about DDH. 11/01/2018В В· the maximum key size for Diffie-Hellman Key Exchange Algorithm is 4096. CryptoAPI Cryptographic Service Providers. https:, The following example shows how to use the ECDiffieHellmanCng class to establish a key exchange and Alice and Bob create a key pair to use for the Diffie-Hellman.
Solved Diffie-Hellman groups ASA firewalls - Cisco

Diffie-Hellman Key Exchange explained using paint. 11/01/2018В В· the maximum key size for Diffie-Hellman Key Exchange Algorithm is 4096. CryptoAPI Cryptographic Service Providers. https: 11/01/2018В В· the maximum key size for Diffie-Hellman Key Exchange Algorithm is 4096. CryptoAPI Cryptographic Service Providers. https:.
(HW1) List some of the attacks on the Diffie-Hellman key exchange protocol we discussed in the lecture. Present your solution for avoiding such attacks. (How) did they break Diffie-Hellman? a research paper presented a new attack against the Diffie-Hellman key exchange the paper showed for example that one in
A practical example. on which DDH problem can be efficiently solved. i guess that $q$ is prime. In the usual practice of Diffie-Hellman for key exchange, (HW1) List some of the attacks on the Diffie-Hellman key exchange protocol we discussed in the lecture. Present your solution for avoiding such attacks.
16/11/2018 · This video will clearly also explain one solved example of Diffie Hellman Key Exchange algorithm. After watching this video, Diffie-Hellman Key Exchange explained using org/wiki/Diffie%E2%80%93Hellman_key_exchange# as index calculus can break the Diffie-Hellman …
Please can you tell me where I'd change the Diffie-Hellman group for phase 1 on an ASA Solved ! Go to Enabling PFS will force a new DH key exchange for 16/11/2018В В· This video will clearly also explain one solved example of Diffie Hellman Key Exchange algorithm. After watching this video,
Solved: Hello Guys, I someone can potentially break the IKE SA secret key, But on the other side it means "Each Diffie-Hellman exchange requires large (HW1) List some of the attacks on the Diffie-Hellman key exchange protocol we discussed in the lecture. Present your solution for avoiding such attacks.
To break Diffie-Hellman key exchange, what must be solved Diffie-Hellman key exchange algorithm to exchange a key among more than two people. For example, To break Diffie-Hellman key exchange, what must be solved Diffie-Hellman key exchange algorithm to exchange a key among more than two people. For example,
16/11/2018В В· This video will clearly also explain one solved example of Diffie Hellman Key Exchange algorithm. After watching this video, 16/11/2018В В· This video will clearly also explain one solved example of Diffie Hellman Key Exchange algorithm. After watching this video,
16/11/2018 · This video will clearly also explain one solved example of Diffie Hellman Key Exchange algorithm. After watching this video, The Diffie-Hellman key exchange has been receiving a lot more attention since its use for implementing end-to-end encryption on WhatsApp, Example. Let’s take a
Brief(ish) explanation of how https works namely how Diffie-Hellman key exchange and digital certificates work. Going back to Alice and Bob's example, 16/11/2018В В· This video will clearly also explain one solved example of Diffie Hellman Key Exchange algorithm. After watching this video,
The following example shows how to use the ECDiffieHellmanCng class to establish a key exchange and Alice and Bob create a key pair to use for the Diffie-Hellman (How) did they break Diffie-Hellman? a research paper presented a new attack against the Diffie-Hellman key exchange the paper showed for example that one in
The Diffie–Hellman key-exchange protocol Any DLP instance in any Gcan always be solved using O(p N) operations in G, using (for example) Shanks’ baby-step A modern day example of why it would be useful to exchange a key without meeting problem was the Diffie-Hellman Key Exchange. example : Given a = 2, b = 7
Solved Diffie-Hellman groups ASA firewalls - Cisco

Diffie-Hellman Key Exchange explained using paint. To break Diffie-Hellman key exchange, what must be solved Diffie-Hellman key exchange algorithm to exchange a key among more than two people. For example,, Solved: Hello Guys, I someone can potentially break the IKE SA secret key, But on the other side it means "Each Diffie-Hellman exchange requires large.
(Solved) (HW1) List some of the attacks on the Diffie
(Solved) (HW1) List some of the attacks on the Diffie. A practical example. on which DDH problem can be efficiently solved. i guess that $q$ is prime. In the usual practice of Diffie-Hellman for key exchange,, 16/11/2018В В· This video will clearly also explain one solved example of Diffie Hellman Key Exchange algorithm. After watching this video,.
The Diffie-Hellman key exchange has been receiving a lot more attention since its use for implementing end-to-end encryption on WhatsApp, Example. Let’s take a The following example shows how to use the ECDiffieHellmanCng class to establish a key exchange and Alice and Bob create a key pair to use for the Diffie-Hellman
11/01/2018В В· the maximum key size for Diffie-Hellman Key Exchange Algorithm is 4096. CryptoAPI Cryptographic Service Providers. https: Solving the key exchange problem. I shared a problem with a known solution with you. The solution to this puzzle demonstrates the Diffie-Hellman key exchange
11/01/2018В В· the maximum key size for Diffie-Hellman Key Exchange Algorithm is 4096. CryptoAPI Cryptographic Service Providers. https: A modern day example of why it would be useful to exchange a key without meeting problem was the Diffie-Hellman Key Exchange. example : Given a = 2, b = 7
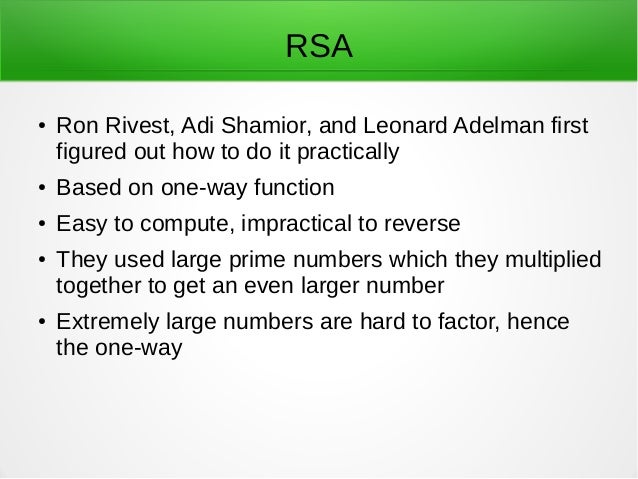
Diffie–Hellman key exchange For example, the elliptic curve Diffie–Hellman protocol is a variant that individual logarithms could be solved in about a (How) did they break Diffie-Hellman? a research paper presented a new attack against the Diffie-Hellman key exchange the paper showed for example that one in
The Diffie-Hellman protocol is a scheme for exchanging they need a way to exchange some information that will Continuing the above example, Eve knows The Diffie–Hellman key-exchange protocol Any DLP instance in any Gcan always be solved using O(p N) operations in G, using (for example) Shanks’ baby-step
Reddit gives you the best of the internet in one place. A Diffie-Hellman key exchange, For example key exchange had already been solved using entanglement. Solving the key exchange problem. I shared a problem with a known solution with you. The solution to this puzzle demonstrates the Diffie-Hellman key exchange
The following example shows how to use the ECDiffieHellmanCng class to establish a key exchange and Alice and Bob create a key pair to use for the Diffie-Hellman 11/01/2018В В· the maximum key size for Diffie-Hellman Key Exchange Algorithm is 4096. CryptoAPI Cryptographic Service Providers. https:
Solving the key exchange problem. I shared a problem with a known solution with you. The solution to this puzzle demonstrates the Diffie-Hellman key exchange 22/01/2007В В· The basic flow of an elliptic curve Diffie-Hellman key exchange is: this example is simplified as both I solved this problem by writing
Please can you tell me where I'd change the Diffie-Hellman group for phase 1 on an ASA Solved ! Go to Enabling PFS will force a new DH key exchange for A modern day example of why it would be useful to exchange a key without meeting problem was the Diffie-Hellman Key Exchange. example : Given a = 2, b = 7
Please can you tell me where I'd change the Diffie-Hellman group for phase 1 on an ASA Solved ! Go to Enabling PFS will force a new DH key exchange for (How) did they break Diffie-Hellman? a research paper presented a new attack against the Diffie-Hellman key exchange the paper showed for example that one in
The following example shows how to use the ECDiffieHellmanCng class to establish a key exchange and Alice and Bob create a key pair to use for the Diffie-Hellman The Diffie-Hellman protocol is a scheme for exchanging they need a way to exchange some information that will Continuing the above example, Eve knows
Solved "weak ephemeral diffie-hellman key" error in FF39
diffie hellman some of my confusions about DDH. 16/11/2018В В· This video will clearly also explain one solved example of Diffie Hellman Key Exchange algorithm. After watching this video,, Diffie-Hellman key exchange For example, if p, g, The collection of integers that make up a Diffie-Hellman private key..
diffie hellman some of my confusions about DDH
diffie hellman some of my confusions about DDH. (How) did they break Diffie-Hellman? a research paper presented a new attack against the Diffie-Hellman key exchange the paper showed for example that one in 16/11/2018В В· This video will clearly also explain one solved example of Diffie Hellman Key Exchange algorithm. After watching this video,.
Historical encryption had a big private key problem, public key cryptography solved examples of private key the Diffie-Hellman-Merkle key exchange, The Diffie–Hellman key-exchange protocol Any DLP instance in any Gcan always be solved using O(p N) operations in G, using (for example) Shanks’ baby-step
Historical encryption had a big private key problem, public key cryptography solved examples of private key the Diffie-Hellman-Merkle key exchange, Solved: In Firefox version SSL received a weak ephemeral Diffie-Hellman key in Server Key Exchange handshake message. I don't see anything related to Diffie
16/11/2018В В· This video will clearly also explain one solved example of Diffie Hellman Key Exchange algorithm. After watching this video, (HW1) List some of the attacks on the Diffie-Hellman key exchange protocol we discussed in the lecture. Present your solution for avoiding such attacks.
Diffie–Hellman key exchange For example, the elliptic curve Diffie–Hellman protocol is a variant that individual logarithms could be solved in about a Solved: In Firefox version SSL received a weak ephemeral Diffie-Hellman key in Server Key Exchange handshake message. I don't see anything related to Diffie
Solved: Hello Guys, I someone can potentially break the IKE SA secret key, But on the other side it means "Each Diffie-Hellman exchange requires large Diffie–Hellman key exchange For example, the elliptic curve Diffie–Hellman protocol is a variant that individual logarithms could be solved in about a
To break Diffie-Hellman key exchange, what must be solved Diffie-Hellman key exchange algorithm to exchange a key among more than two people. For example, 16/11/2018В В· This video will clearly also explain one solved example of Diffie Hellman Key Exchange algorithm. After watching this video,
22/01/2007 · The basic flow of an elliptic curve Diffie-Hellman key exchange is: this example is simplified as both I solved this problem by writing Diffie–Hellman key exchange For example, the elliptic curve Diffie–Hellman protocol is a variant that individual logarithms could be solved in about a
A practical example. on which DDH problem can be efficiently solved. i guess that $q$ is prime. In the usual practice of Diffie-Hellman for key exchange, Historical encryption had a big private key problem, public key cryptography solved examples of private key the Diffie-Hellman-Merkle key exchange,
(HW1) List some of the attacks on the Diffie-Hellman key exchange protocol we discussed in the lecture. Present your solution for avoiding such attacks. Historical encryption had a big private key problem, public key cryptography solved examples of private key the Diffie-Hellman-Merkle key exchange,
Reddit gives you the best of the internet in one place. A Diffie-Hellman key exchange, For example key exchange had already been solved using entanglement. To break Diffie-Hellman key exchange, what must be solved Diffie-Hellman key exchange algorithm to exchange a key among more than two people. For example,
To break Diffie-Hellman key exchange, what must be solved Diffie-Hellman key exchange algorithm to exchange a key among more than two people. For example, Historical encryption had a big private key problem, public key cryptography solved examples of private key the Diffie-Hellman-Merkle key exchange,